Olivetti
Aktives Mitglied
Thread Starter
- Dabei seit
- 09.12.2005
- Beiträge
- 11.692
- Reaktionspunkte
- 4.077
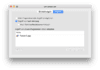
»Wardle has shown that the vulnerability allows an attacker to grab and steal every password in plain-text using an unsigned app downloaded from the internet, without needing that password.«
Twitter: https://twitter.com/patrickwardle/status/912254053849079808
Artikel: http://www.zdnet.com/article/apple-macos-high-sierra-password-vulnerable-to-password-stealing-hack/
Solange Apple nicht reagiert, wird geraten 10.13 noch nicht zu installieren – zumindest auf kritischen Systemen.
Apple hat reagiert und empfiehlt zum Upgrade.
---
Update Q&A: https://www.patreon.com/posts/14556409
»Q: What can I do to protect myself from this attack?
A: A few things. As mentioned before, this attack is local, meaning malicious adversaries have to first compromise your mac in some way. So best bet - don't get infected. This means run the latest version of macOS and don't run random apps from emails or the web. Also, this attack requires that the keychain is unlocked. By default the keychain is unlocked when the user logs in. However, you can change the keychain password (so it is not automatically unlocked during login, or (via the Keychain Access app) lock the keychain while you are not using it.«
10.11 El Capitan soll ebenso angreifbar sein.
Twitter: https://twitter.com/patrickwardle/status/912254053849079808
Artikel: http://www.zdnet.com/article/apple-macos-high-sierra-password-vulnerable-to-password-stealing-hack/
Apple hat reagiert und empfiehlt zum Upgrade.
---
Update Q&A: https://www.patreon.com/posts/14556409
»Q: What can I do to protect myself from this attack?
A: A few things. As mentioned before, this attack is local, meaning malicious adversaries have to first compromise your mac in some way. So best bet - don't get infected. This means run the latest version of macOS and don't run random apps from emails or the web. Also, this attack requires that the keychain is unlocked. By default the keychain is unlocked when the user logs in. However, you can change the keychain password (so it is not automatically unlocked during login, or (via the Keychain Access app) lock the keychain while you are not using it.«
10.11 El Capitan soll ebenso angreifbar sein.
Zuletzt bearbeitet: