akumetsu
Aktives Mitglied
Thread Starter
- Dabei seit
- 19.08.2011
- Beiträge
- 2.925
- Reaktionspunkte
- 1.181
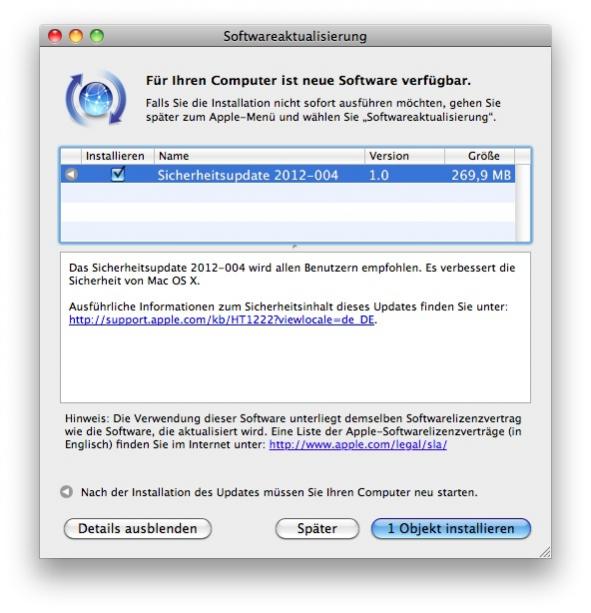
Gestern ist auch das Sicherheitsupdate 2012-004 für 10.6.8 erschienen!
Supportdokument dazu: http://support.apple.com/kb/HT5501
Es sieht also so aus als würde Apple nun wirklich die letzten drei Systeme mit Updates versorgen. Ich hatte mich eigentlich schon damit abgefunden ein nicht weiter unterstütztes System zu benutzen aber anscheinend kann man hoffen, dass SL bis zum Erscheinen vom ML-Nachfolger 10.9 versorgt wird.
Und hier noch die bereinigte Liste der Änderungen für SL:
Supportdokument dazu: http://support.apple.com/kb/HT5501
Es sieht also so aus als würde Apple nun wirklich die letzten drei Systeme mit Updates versorgen. Ich hatte mich eigentlich schon damit abgefunden ein nicht weiter unterstütztes System zu benutzen aber anscheinend kann man hoffen, dass SL bis zum Erscheinen vom ML-Nachfolger 10.9 versorgt wird.
Und hier noch die bereinigte Liste der Änderungen für SL:
Data Security
Impact: An attacker with a privileged network position may intercept user credentials or other sensitive information
Description: TrustWave, a trusted root CA, has issued, and subsequently revoked, a sub-CA certificate from one of its trusted anchors. This sub-CA facilitated the interception of communications secured by Transport Layer Security (TLS). This update adds the involved sub-CA certificate to OS X's list of untrusted certificates.
DirectoryService
Impact: If the DirectoryService Proxy is used, a remote attacker may cause a denial of service or arbitrary code execution
Description: A buffer overflow existed in the DirectoryService Proxy. This issue was addressed through improved bounds checking. This issue does not affect OS X Lion and Mountain Lion systems.
ImageIO
Impact: Viewing a maliciously crafted PNG image may lead to an unexpected application termination or arbitrary code execution
Description: Multiple memory corruption issues existed in libpng's handling of PNG images. These issues were addressed through improved validation of PNG images. These issues do not affect OS X Mountain Lion systems.
ImageIO
Impact: Viewing a maliciously crafted TIFF image may lead to an unexpected application termination or arbitrary code execution
Description: An integer overflow issue existed in libTIFF's handling of TIFF images. This issue was addressed through improved validation of TIFF images. This issue does not affect OS X Mountain Lion systems.
International Components for Unicode
Impact: Applications that use ICU may be vulnerable to an unexpected application termination or arbitrary code execution
Description: A stack buffer overflow existed in the handling of ICU locale IDs. This issue was addressed through improved bounds checking. This issue does not affect OS X Mountain Lion systems.
Impact: Viewing an e-mail message may lead to execution of web plugins
Description: An input validation error existed in Mail's handling of embedded web plugins. This issue was addressed by disabling third-party plug-ins in Mail. This issue does not affect OS X Mountain Lion systems.
PHP
Impact: Multiple vulnerabilities in PHP
Description: >PHP is updated to version 5.3.15 to address multiple vulnerabilities, the most serious of which may lead to arbitrary code execution. Further information is available via the PHP web site at http://www.php.net
PHP
Impact: PHP scripts which use libpng may be vulnerable to an unexpected application termination or arbitrary code execution
Description: A memory corruption issue existed in the handling of PNG files. This issue was addressed by updating PHP's copy of libpng to version 1.5.10. This issue does not affect OS X Mountain Lion systems.
QuickLook
Impact: Viewing a maliciously crafted .pict file may lead to an unexpected application termination or arbitrary code execution
Description: A memory corruption issue existed in the handling of .pict files. This issue was addressed through improved validation of .pict files. This issue does not affect OS X Mountain Lion systems.
QuickTime
Impact: Viewing a maliciously crafted movie file may lead to an unexpected application termination or arbitrary code execution
Description: An integer overflow existed in QuickTime's handling of sean atoms. This issue was addressed through improved bounds checking. This issue does not affect OS X Mountain Lion systems.
QuickTime
Impact: Viewing a maliciously crafted movie file may lead to an unexpected application termination or arbitrary code execution
Description: An uninitialized memory access existed in the handling of Sorenson encoded movie files. This issue was addressed through improved memory initialization. This issue does not affect OS X Mountain Lion systems.
QuickTime
Impact: Viewing a maliciously crafted movie file may lead to an unexpected application termination or arbitrary code execution
Description: A buffer overflow existed in the handling of RLE encoded movie files. This issue was addressed through improved bounds checking. This issue does not affect OS X Mountain Lion systems.
Ruby
Impact: An attacker may be able to decrypt data protected by SSL
Description: There are known attacks on the confidentiality of SSL 3.0 and TLS 1.0 when a cipher suite uses a block cipher in CBC mode. The Ruby OpenSSL module disabled the 'empty fragment' countermeasure which prevented these attacks. This issue was addressed by enabling empty fragments. This issue does not affect OS X Mountain Lion systems.



 aber nicht von 2011/2012 usw.
aber nicht von 2011/2012 usw.  …versteh ich jetzt nicht…wenn ich dort auf „laden“ klicke, beginnt der Download des DMGs.
…versteh ich jetzt nicht…wenn ich dort auf „laden“ klicke, beginnt der Download des DMGs.